How do you fix SHA-1 cipher suites were detected?
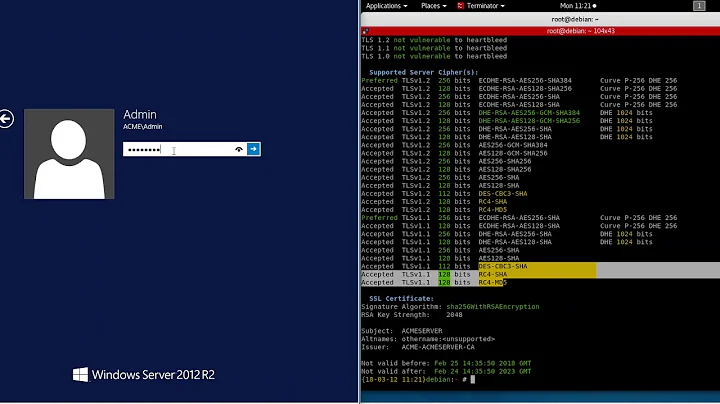
In the vulnerability “SHA-1 cipher suites were detected” the fix recommendation includes ciphers that are now considered “Old backward compatibility” and no longer “Modern compatibility” and require updating.
Disable RC4/DES/3DES cipher suites in Windows using registry, GPO, or local security settings. You can do this using GPO or Local security policy under Computer configuration -> Administrative Templates -> Network -> SSL Configuration Settings -> SSL Cipher Suite Order. Set this policy to enable.
Disabling TLS 1.0 and 1.1
It also strongly suggests that you disable TLS 1.1. These protocols may be affected by vulnerabilities such as FREAK, POODLE, BEAST, and CRIME. If you must still support TLS 1.0, disable TLS 1.0 compression to avoid CRIME attacks. You should also disable weak ciphers such as DES and RC4.
- Log in to the sensor with the root account via SSH or console connection.
- Edit the /etc/ssh/sshd_config file and add the following line: Ciphers aes128-ctr,aes192-ctr,aes256-ctr,aes128-cbc,3des-cbc,blowfish-cbc,cast128-cbc,aes192-cbc,aes256-cbc.
- Restart the sshd service to make the changes take effect:
- At a command prompt, enter gpedit. ...
- Go to Computer Configuration > Administrative Templates > Network > SSL Configuration Settings.
- Under SSL Configuration Settings, select SSL Cipher Suite Order.
- In the SSL Cipher Suite Order pane, scroll to the bottom.
If you go to a secure website or service using Chrome you can see which cipher suite was negotiated. Any HTTPS site will give you this information. At the top of the developer tools window, you will see a tab called security. Click it.
Disabling specific protocols and cipher suites makes your Code42 environment more secure against attacks designed to exploit these vulnerabilities.
The Disable-TlsCipherSuite cmdlet disables a cipher suite. This cmdlet removes the cipher suite from the list of Transport Layer Security (TLS) protocol cipher suites for the computer.
- Open Registry Editor. ...
- Navigate to Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols.
- Select Protocols and in the right pane, right-click the empty space. ...
- Create a new key as already explained, and name it TLS 1.1.
On the left hand side, expand Computer Configuration, Administrative Templates, Network, and then click on SSL Configuration Settings. On the right hand side, double click on SSL Cipher Suite Order. By default, the “Not Configured” button is selected. Click on the “Enabled” button to edit your server's Cipher Suites.
How do I add a cipher suite?
To add cipher suites, either deploy a group policy or use the TLS cmdlets: To use group policy, configure SSL Cipher Suite Order under Computer Configuration > Administrative Templates > Network > SSL Configuration Settings with the priority list for all cipher suites you want enabled.
- # openssl ciphers -help. usage: ciphers args. -v – verbose mode, a textual listing of the SSL/TLS ciphers in OpenSSL. ...
- # openssl ciphers -v. ECDHE-RSA-AES256-GCM-SHA384 TLSv1.2 Kx=ECDH Au=RSA Enc=AESGCM(256) Mac=AEAD. ...
- PORT STATE SERVICE. 5432/tcp open postgresql.
- Launch Chrome.
- Enter the URL you wish to check in the browser.
- Click on the ellipsis located on the top-right in the browser.
- Select More tools > Developer tools > Security.
- Look for the line "Connection...". This will describe the version of TLS or SSL used.
To add cipher suites, either deploy a group policy or use the TLS cmdlets: To use group policy, configure SSL Cipher Suite Order under Computer Configuration > Administrative Templates > Network > SSL Configuration Settings with the priority list for all cipher suites you want enabled.
Definition: Cipher is an algorithm which is applied to plain text to get ciphertext. It is the unreadable output of an encryption algorithm. The term "cipher" is sometimes used as an alternative term for ciphertext. Ciphertext is not understandable until it has been converted into plain text using a key.
Cipher suites are sets of instructions that enable secure network connections through Transport Layer Security (TLS), often still referred to as Secure Sockets Layer (SSL). Behind the scenes, these cipher suites provide a set of algorithms and protocols required to secure communications between clients and servers.
- Click the padlock icon in the address bar for the website.
- Click on Certificate (Valid) in the pop-up.
- Check the Valid from dates to validate the SSL certificate is current.
- Open Google Chrome.
- Click Alt F and select Settings.
- Scroll down and select Show advanced settings...
- Scroll down to the Network section and click on Change proxy settings...
- Select the Advanced tab.
- Scroll down to Security category, manually check the option boxes for Use TLS 1.0,Use TLS 1.1 and Use TLS 1.2.
1. Within the browser window, click on Tools -> Internet Options 2. Click on the Advanced tab 3. Scroll to the bottom and check the TLS version described in steps 3 and 4: 4.
One of the most secure encryption types, Advanced Encryption Standard (AES) is used by governments and security organizations as well as everyday businesses for classified communications. AES uses “symmetric” key encryption.
Which SSL version is secure?
TLS, the more modern version of SSL, is secure. What's more, recent versions of TLS also offer performance benefits and other improvements. Not only is TLS more secure and performant, most modern web browsers no longer support SSL 2.0 and SSL 3.0.
- You can do this using GPO or Local security policy under Computer configuration -> Administrative Templates -> Network -> SSL Configuration Settings -> SSL Cipher Suite Order.
- Set this policy to enable.
To disable SSL compression, set the following directive in your SSL settings: usually /etc/apache2/mods-enabled/ssl. confor /etc/letsencrypt/options-ssl-apache.
- Open Google Chrome.
- Click Alt F and select Settings.
- Scroll down and select Show advanced settings...
- Scroll down to the System section and click on Open proxy settings...
- Select the Advanced tab.
- Scroll down to the Security category, manually check the option box for Use TLS 1.2.
Right-click on Protocol, select New > Key, and name it “TLS 1.0″. Now, right-click on TLS 1.0, select New > Key, and name it “Client”. Right-click on Client, select New > DWORD (32-bit) Value, and name it “Enabled”. Now, since the default value of Enabled is 0, TLS 1.0 will be disabled.
However, due to evolving regulatory requirements as well as new security vulnerabilities in TLS 1.0, Microsoft recommends that customers remove TLS 1.0/1.1 dependencies in their environments and disable TLS 1.0 and 1.1 at the operating system level where possible.
- Update Windows and WinHTTP.
- Ensure that TLS 1.2 is enabled as a protocol for SChannel at the operating system level.
- Update and configure the . NET Framework to support TLS 1.2.
The quickest way to check whether TLS 1.2 is enabled on your computer is to search for the presence of the registry key. HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client\Enabled And its corresponding value, 1.
- Log into the server via SSH.
- Execute the command: # nmap --script ssl-enum-ciphers -p 443 example.com | grep -E "TLSv|SSLv" Note: replace the example.com with the name of the required domain. The output will be as shown below: # | SSLv3: No supported ciphers found. | TLSv1.0: | TLSv1.1: | TLSv1.2:
- Run the following command to remove TLS 1.0 from SSL protocol: sudo sed -i 's/TLSv1 //' /etc/nginx/conf.d/ssfe.conf.
- Confirm the changes in the SSL protocol using the command below: ...
- Restart the ngix service for the changes to take effect: ...
- Test the new configuration using the SSL Server Test website.
How do I know if SSL is open?
- Click the Windows "Start" button and type "cmd" into the search text box. ...
- Type "openssl /?" to view a list of options for the command line utility. ...
- Type "openssl version" and press "Enter." The OpenSSL version is displayed in the Windows command line utility.
- Open Registry Editor. ...
- Navigate to Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols.
- Select Protocols and in the right pane, right-click the empty space. ...
- Create a new key as already explained, and name it TLS 1.1.
- To remove ssl-anon-ciphers, you will need to add ! aNULL in the httpd configuration.
- To remove ssl-null-ciphers, you will need to add ! eNULL in the httpd configuration.
- Log in to tmsh by typing the following command: ...
- List the currently configured SSL protocols. ...
- Explicitly disable the CBC cipher by adding the :! ...
- Verify the change was made to the running configuration.
- At a command prompt, type gpedit. ...
- Expand Computer Configuration, Administrative Templates, Network, and then click SSL Configuration Settings.