How do I copy my public PGP key?
- Open PGP Desktop.
- Click "PGP Keys".
- Right-click the key to export, then select Copy Public Key.
- Also paste the key block of the public key to a text file as an additional backup.
You can download my PGP key or find it below. But the best way to obtain my key is to get it from a keyserver like hkp://subkeys.pgp.net or ldap://keyserver.pgp.com. If you do not have access to a keyserver, you can: First save the entire PGP block into a file (click on Grab), which we'll call ybrailowsky.
GPG can decrypt PGP files because it is a tool that conforms to the OpenPGP standard. Any message that is encrypted in the OpenPGP format can be decrypted by GPG — or by any other standard conforming tool, such as Diplomat MFT.
- Select GnuPG keys from the left side panel.
- From the list, select the Personal PGP key you want to publish.
- Select Remote ▸ Sync and Publish Keys….
- Press the Key Servers button to see the list of key servers on which you can publish your public key.
To export your public PGP key
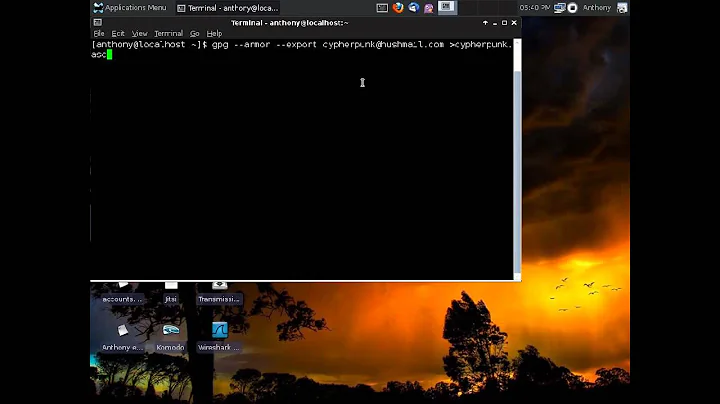
Select the GnuPG keys keyring from the left side panel. Select the Personal PGP key that has to be exported, from the list. Select File ▸ Export…. To store the keys in the ASCII format, select Armored PGP keys from the menu above the Export button.
Another way to find someone's public key is to download it from a keyserver. Select Keyserver → Search for keys and insert as the search term a part of the name or email address of this person. You may also search for key IDs. The keyserver will return a list of public keys that match.
- Open the e-mail containing the encrypted message in ciphertext.
- Highlight the block of ciphertext.
- Open the PGP Tray.
- Select Current Window. Choose Decrypt & Verify.
- Enter a passphrase into the PGP Enter Passphrase dialog box. Click OK.
- The decrypted message will come up in a new window for you to read.
- Open Encryption Desktop.
- Select the PGP Keys Control box.
- Click the File > New > PGP Key.
- When the Key Generation Assistant appears, click Next. ...
- Enter a Full Name and Primary Email address for the key.
PGP uses key IDs to refer to public keys for a variety of purposes. These are not, properly speaking, fingerprints, since their short length prevents them from being able to securely authenticate a public key. 32bit key ids should not be used as current hardware can generate a colliding 32bit key id in just 4 seconds.
80-bit key: One year of brute-forcing after 30 years of tech improvement (or roughly 33 thousand years with today's tech). 96-bit key: One year of brute-forcing after 62 years of tech improvement (or over two billion years with today's tech).
Has PGP been hacked?
Is PGP Encryption Secure? PGP encryption is almost impossible to hack. That's why it's still used by entities that send and receive sensitive information, such as journalists and hacktivists. Though PGP encryption cannot be hacked, OpenPGP does have a vulnerability that disrupts PGP encrypted messages when exploited.
Since version 2.1, PGP ("Pretty Good Privacy") has been rigged to allow the NSA to easily break encoded messages.
- Get your trading partner's public key to encrypt the file.
- Import your trading partner's public key into a Key Vault.
- Use your file transfer tool to create a Project to encrypt the file.
- Confirm that the project was set up correctly before executing.
All GPG keys are stored in the "keyring", which is at ~/. gnupg or %AppData%/gnupg . Running gpg --version will show the path being used. The usual way of sharing keys is to export them to a file...
Importing public certificates into Kleopatra
To do this, start Kleopatra if the program is not running already. In the menu, click on File -> Import certificate..., search for the public certificate you have just saved and import it.