How do I disable weak ciphers in registry?
To turn off encryption (disallow all cipher algorithms), change the DWORD value data of the Enabled value to 0xffffffff. Otherwise, change the DWORD value data to 0x0. The Hashes registry key under the SCHANNEL key is used to control the use of hashing algorithms such as SHA-1 and MD5.
go to HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Server ; create the key if it does not exist. make sure that DWORD value Enabled exists and is set it to 1. make sure that DWORD value DisabledByDefault (if exists) is set it to 0.
- In a text editor, open the following file: [app-path]/server/server.properties.
- Locate the line starting with “server.ssl.using-strong-defaults”
- Remove the proceeding # sign to uncomment the lines and edit the list as needed.
- Restart the server using the node.restart command: node.restart.
- To verify the new cipher settings in your Code42 environment, enter the prop. show c42. ...
- Verify that the cipher exclusion works as expected by running an analysis on your Code42 server of the protocols and cipher suites in use.
This cipher suite's registry keys are located here: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\
- Start the registry editor by clicking on Start and Run. ...
- Highlight Computer at the top of the registry tree. ...
- Browse to the following registry key: ...
- Right click on the Protocols folder and select New and then Key from the drop-down menu. ...
- Right click on the TLS 1.2 key and add two new keys underneath it.
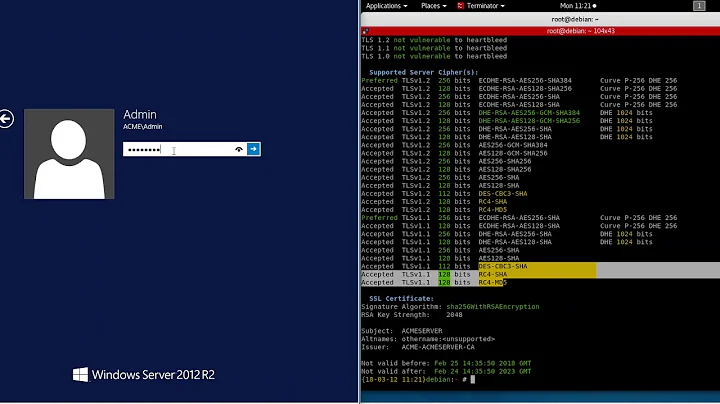
Disabling TLS 1.0 and 1.1
It also strongly suggests that you disable TLS 1.1. These protocols may be affected by vulnerabilities such as FREAK, POODLE, BEAST, and CRIME. If you must still support TLS 1.0, disable TLS 1.0 compression to avoid CRIME attacks. You should also disable weak ciphers such as DES and RC4.
Weak Cipher Definition. A weak cipher is defined as an encryption/decryption algorithm that uses a key of insufficient length. Using an insufficient length for a key in an encryption/decryption algorithm opens up the possibility (or probability) that the encryption scheme could be broken (i.e. cracked).
How to Disable TLS 1.0 in Windows 11/10 - YouTube
Successful brute-forcing of weak ciphers can result in a malicious actor decrypting data containing sensitive information, potentially leading to a complete compromise of confidentiality and integrity. The extent of damage is really only limited to the value of compromised data and the imagination of the attacker.
How do I enable strong ciphers?
- Verify the manager using nmap. Run this command: nmap --script ssl-enum-ciphers -p 4119 <Manager_FQDN> ...
- Verify the relays using nmap. Run this command: nmap --script ssl-enum-ciphers -p 4122 <Relay_FQDN> ...
- Verify the agents using nmap. Run this command: nmap --script ssl-enum-ciphers -p 4118 <Agent_FQDN>
Ultimately, it is recommended to configure the server to only support strong ciphers and to use sufficiently large public key sizes. Your organization should avoid TLS versions 1.1 and below and RC4 encryption, as there have been multiple vulnerabilities discovered that render it insecure.
- From the Group Policy Management Console, go to Computer Configuration > Administrative Templates > Network > SSL Configuration Settings.
- Double-click SSL Cipher Suite Order, and then click the Enabled option.
- Log in to the sensor with the root account via SSH or console connection.
- Edit the /etc/ssh/sshd_config file and add the following line: Ciphers aes128-ctr,aes192-ctr,aes256-ctr,aes128-cbc,3des-cbc,blowfish-cbc,cast128-cbc,aes192-cbc,aes256-cbc.
- Restart the sshd service to make the changes take effect:
- Open Registry Editor. ...
- Navigate to Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols.
- Select Protocols and in the right pane, right-click the empty space. ...
- Create a new key as already explained, and name it TLS 1.1.
- Launch Internet Explorer.
- Enter the URL you wish to check in the browser.
- Right-click the page or select the Page drop-down menu, and select Properties.
- In the new window, look for the Connection section. This will describe the version of TLS or SSL used.
- Open regedit.exe and go to: HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Cryptography\Configuration\Local\SSL\00010002.
- Edit the Functions key, and set its value to the list of Cipher Suites that you want to allow. ...
- Restart the PVWA server.
- Open Google Chrome.
- Click Alt F and select Settings.
- Scroll down and select Show advanced settings...
- Scroll down to the Network section and click on Change proxy settings...
- Select the Advanced tab.
- Scroll down to Security category, manually check the option boxes for Use TLS 1.0,Use TLS 1.1 and Use TLS 1.2.
- Click Start or press the Windows key.
- In the Start menu, either in the Run box or the Search box, type regedit and press Enter. ...
- Navigate to follow the registry path: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols.
If the registry key HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client\Enabled is present, value should be 1. Check if TLS 1.2 is set as the default secure protocol in WinHTTP for Windows versions Windows Server 2008 R2, Windows Server 2012, and Windows 7.
How do I find TLS settings in Windows 10?
Click on: Start -> Control Panel -> Internet Options 2. Click on the Advanced tab 3. Scroll to the bottom and check the TLS version described in steps 3 and 4: 4. If Use SSL 2.0 is enabled, you must have TLS 1.2 enabled (checked) 5.
Disable TLS 1.0 or 1.1 via Registry
Create a new subkey called "TLS 1.0 or 1.1" under Protocols. Create a new subkey called "Server" under TLS 1.0 or 1.1. In the Server key, create a DWORD DisabledByDefault entry, set the value to 1. Reboot the server.
In the Internet Options window on the Advanced tab, under Settings, scroll down to the Security section. In the Security section, locate the Use SSL and Use TLS options and uncheck Use SSL 3.0 and Use SSL 2.0.
...
The steps:
- vi /etc/ssh/shh_config.
- Replace #Cyphers line with: Ciphers aes128-ctr,aes192-ctr,aes256-ctr,arcfour256,arcfour128.
- Replace #MACs line with: MACs hmac-sha1,umac-64@openssh.com,hmac-ripemd160.
- Esc --> : --> :wq.
- Log in to the sensor with the root account via SSH or console connection.
- Edit the /etc/ssh/sshd_config file and add the following line: Ciphers aes128-ctr,aes192-ctr,aes256-ctr,aes128-cbc,3des-cbc,blowfish-cbc,cast128-cbc,aes192-cbc,aes256-cbc.
- Restart the sshd service to make the changes take effect:
We can disable 3DES and RC4 ciphers by removing them from registry HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Cryptography\Configuration\Local\SSL\00010002 and then restart the server.
- Login with root. Take a copy of the /etc/ssh/sshd_config file on your local system.
- Edit the /etc/ssh/sshd_config file: a. Comment out the line starting with "Ciphers" (if exists) by inserting the # symbol at the beginning of line. b. ...
- Run: service sshd restart. Related Answers.
- Step 1: Edit /etc/sysconfig/sshd and uncomment the following line. ...
- Step 2: Copy the following ciphers, MACs, and KexAlgorithms to /etc/ssh/sshd_config . ...
- Step 3: Verify the configuration file before restarting the SSH server.
...
| SSH Key Exchanges | SSH Ciphers | HMAC |
|---|---|---|
| diffie-hellman-group-exchange-sha1 | 3des-cbc | HMAC-SHA1 |
| diffie-hellman-group1-sha1 |
- # openssl ciphers -help. usage: ciphers args. -v – verbose mode, a textual listing of the SSL/TLS ciphers in OpenSSL. ...
- # openssl ciphers -v. ECDHE-RSA-AES256-GCM-SHA384 TLSv1.2 Kx=ECDH Au=RSA Enc=AESGCM(256) Mac=AEAD. ...
- PORT STATE SERVICE. 5432/tcp open postgresql.
How do I disable Triple DES ciphers?
Disable RC4/DES/3DES cipher suites in Windows using registry, GPO, or local security settings. You can do this using GPO or Local security policy under Computer configuration -> Administrative Templates -> Network -> SSL Configuration Settings -> SSL Cipher Suite Order. Set this policy to enable.
Remove Legacy Ciphers SSL3, DES, 3DES, MD5 and RC4 from SSL Profile. Configuration tab > System > Profiles > SSL Profle Tab > <profile name to be modified> > Edit. Select SSL Ciphers > Add > Select Cipher > uncheck SSL3, DES, MD5, RC4 Ciphers > Move the selected ones under configured.
SSL stands for Secure Sockets Layer and was originally created by Netscape. SSLv2 and SSLv3 are the 2 versions of this protocol (SSLv1 was never publicly released). After SSLv3, SSL was renamed to TLS. TLS stands for Transport Layer Security and started with TLSv1. 0 which is an upgraded version of SSLv3.