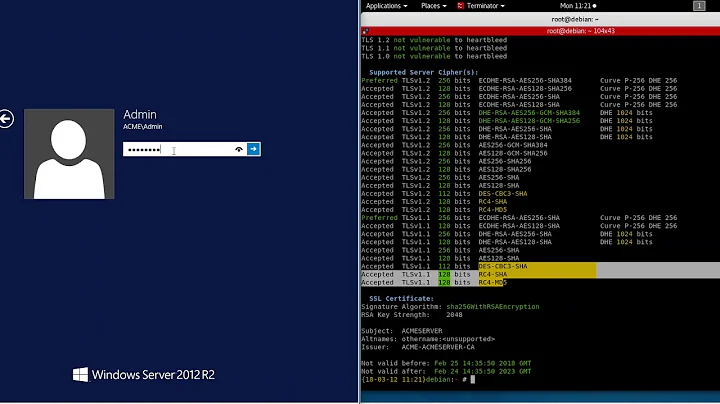
How do I disable Triple DES cipher?
We can disable 3DES and RC4 ciphers by removing them from registry HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Cryptography\Configuration\Local\SSL\00010002 and then restart the server.
- Backup transportprovider. ...
- Login to GUI of Command Center.
- Go to Administration >> Change Cipher Settings.
- Remove the 3DES Ciphers: ...
- Save the configuration.
- Restart the CC Service using following command :
- Restart the server using the node.restart command: node.restart.
- To verify the new cipher settings in your Code42 environment, enter the prop. show c42. ...
- Verify that the cipher exclusion works as expected by running an analysis on your Code42 server of the protocols and cipher suites in use.
Triple DES 168
To allow this cipher algorithm, change the DWORD value data of the Enabled value to 0xffffffff. Or, change the DWORD data to 0x0. If you do not configure the Enabled value, the default is enabled.
- Make the following update to the java.security file: Add the entries below with the SSL_ prefix to the entry for jdk.tls.disabledAlgorithms : ...
- Restart the Impact server.
- Use nmap to retrieve the list of active ciphers:
- # openssl ciphers -help. usage: ciphers args. -v – verbose mode, a textual listing of the SSL/TLS ciphers in OpenSSL. ...
- # openssl ciphers -v. ECDHE-RSA-AES256-GCM-SHA384 TLSv1.2 Kx=ECDH Au=RSA Enc=AESGCM(256) Mac=AEAD. ...
- PORT STATE SERVICE. 5432/tcp open postgresql.
Disable RC4/DES/3DES cipher suites in Windows using registry, GPO, or local security settings. You can do this using GPO or Local security policy under Computer configuration -> Administrative Templates -> Network -> SSL Configuration Settings -> SSL Cipher Suite Order. Set this policy to enable.
- SSL protocol version v2, v3 and PCT v1.
- Symmetric ciphers with keys shorter than 128bit (also known as export ciphers)
- Weak ciphers - like RC2, RC4.
- Weak hash functions - like MD5.
- Log in to the sensor with the root account via SSH or console connection.
- Edit the /etc/ssh/sshd_config file and add the following line: Ciphers aes128-ctr,aes192-ctr,aes256-ctr,aes128-cbc,3des-cbc,blowfish-cbc,cast128-cbc,aes192-cbc,aes256-cbc.
- Restart the sshd service to make the changes take effect:
In the run dialogue box, type “gpedit. msc” and click “o*k” to launch the Group Policy Editor. On the left hand side, expand "Computer Configuration", "Administrative Templates", "Network", and click on "SSL Configuration Settings". On the right hand side, click on "SSL Cipher Suite Order".
How do I disable cipher suites in IIS?
- Create a new key called RC4 128/128 (Ciphers > New > KeyRC4 128/128).
- Right-click the key's name and create a new DWORD (32-bit) Value called 'Enabled'. (New > DWORD (32-bit) Value > Enabled).
- Leave the default value as '0'.
In cryptography, Triple DES (3DES or TDES), officially the Triple Data Encryption Algorithm (TDEA or Triple DEA), is a symmetric-key block cipher, which applies the DES cipher algorithm three times to each data block.
Short answer, No. The short answer with supporting evidence is no, because it has been deprecated by the NIST since 2017 for new applications and for all applications by 2023. It has been superseded by the more robust and longer key lengths of AES.
The Disable-TlsCipherSuite cmdlet disables a cipher suite. This cmdlet removes the cipher suite from the list of Transport Layer Security (TLS) protocol cipher suites for the computer.
- Log in to tmsh by typing the following command: ...
- List the currently configured SSL protocols. ...
- Explicitly disable the CBC cipher by adding the :! ...
- Verify the change was made to the running configuration.
If you go to a secure website or service using Chrome you can see which cipher suite was negotiated. Any HTTPS site will give you this information. At the top of the developer tools window, you will see a tab called security. Click it.
- Launch Chrome.
- Enter the URL you wish to check in the browser.
- Click on the ellipsis located on the top-right in the browser.
- Select More tools > Developer tools > Security.
- Look for the line "Connection...". This will describe the version of TLS or SSL used.
- Make a backup of ssl.conf and edit the original. Satellite 5.2 and earlier: /etc/rhn/satellite-httpd/conf.d/ssl.conf. ...
- Comment out (by prefixing with "#"), or remove entries for SSLProtocol.
- Disable weak encryption by including the following line. SSLProtocol all -SSLv2 -SSLv3.
- Restart httpd:
A cipher uses a system of fixed rules -- an encryption algorithm -- to transform plaintext, a legible message, into ciphertext, an apparently random string of characters. Ciphers can be designed to encrypt or decrypt bits in a stream, known as stream ciphers.
...
Responses
- vi /etc/ssh/shh_config.
- Replace #Cyphers line with: Ciphers aes128-ctr,aes192-ctr,aes256-ctr,arcfour256,arcfour128.
- Replace #MACs line with: MACs hmac-sha1,umac-64@openssh.com,hmac-ripemd160.
- Esc --> : --> :wq.
Which ciphers are weak?
Weak ciphers are generally known as encryption/ decryption algorithms that use key sizes that are less than 128 bits (i.e., 16 bytes … 8 bits in a byte) in length. To understand the ramifications of insufficient key length in an encryption scheme, a little background is needed in basic cryptography.
AES encryption
One of the most secure encryption types, Advanced Encryption Standard (AES) is used by governments and security organizations as well as everyday businesses for classified communications.
Currently, the most secure and most recommended combination of these four is: Elliptic Curve Diffie–Hellman (ECDH), Elliptic Curve Digital Signature Algorithm (ECDSA), AES 256 in Galois Counter Mode (AES256-GCM), and SHA384. See the full list of ciphers supported by OpenSSL.
- Step 1: Edit /etc/sysconfig/sshd and uncomment the following line. ...
- Step 2: Copy the following ciphers, MACs, and KexAlgorithms to /etc/ssh/sshd_config . ...
- Step 3: Verify the configuration file before restarting the SSH server.
SSH is a network protocol that provides secure access to a remote device. client. Cipher Suites for ClearPass as SSH Server lists the cipher suites supported when Policy Manager acts as an SSH. SSH is a network protocol that provides secure access to a remote device.
SSH can be configured to use a variety of different symmetrical cipher systems, including Advanced Encryption Standard (AES), Blowfish, 3DES, CAST128, and Arcfour. The server and client can both decide on a list of their supported ciphers, ordered by preference.
This cipher suite's registry keys are located here: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\
- From the Group Policy Management Console, go to Computer Configuration > Administrative Templates > Network > SSL Configuration Settings.
- Double-click SSL Cipher Suite Order, and then click the Enabled option.
On the left hand side, expand Computer Configuration, Administrative Templates, Network, and then click on SSL Configuration Settings. On the right hand side, double click on SSL Cipher Suite Order. By default, the “Not Configured” button is selected. Click on the “Enabled” button to edit your server's Cipher Suites.
View and Edit Enabled Ciphers
On the left pane, click Computer Configuration >> Administrative Templates >> Network >> SSL Configuration Settings.
How do I check my TLS settings?
Click on: Start -> Control Panel -> Internet Options 2. Click on the Advanced tab 3. Scroll to the bottom and check the TLS version described in steps 3 and 4: 4. If Use SSL 2.0 is enabled, you must have TLS 1.2 enabled (checked) 5.
The Data Encryption Standard, also known as DES, is no longer considered secure. While there are no known severe weaknesses in its internals, it is inherently flawed because its 56-bit key is too short.
What is a downside to using Triple DES? requires more processing time. What is the most likely weak link when using asymmetric encryption for verifying message integrity and nonrepudiation? the source of the public keys.
Triple DES encryption process
It works by taking three 56-bit keys (K1, K2 and K3), and encrypting first with K1, decrypting next with K2 and encrypting a last time with K3. 3DES has two-key and three-key versions. In the two-key version, the same algorithm runs three times, but uses K1 for the first and last steps.
But Christof Paar at Ruhr-University Bochum has led a team that hacked 3DES using a low-cost system to break in with just a few hours of work.
According to draft guidance published by NIST on July 19, 2018, the Triple Data Encryption Algorithm (TDEA or 3DES) is officially being retired. The guidelines propose that, after a period of public consultation, 3DES is deprecated for all new applications and usage is disallowed after 2023.
Since Triple DES uses two keys, the effective key length is 112 bits. This is a lot more secure. If you could break DES by brute-force in one second (which is very far from being the case) then it would take 2.285 billion years to break Triple DES.
- Make a backup of ssl.conf and edit the original. Satellite 5.2 and earlier: /etc/rhn/satellite-httpd/conf.d/ssl.conf. ...
- Comment out (by prefixing with "#"), or remove entries for SSLProtocol.
- Disable weak encryption by including the following line. SSLProtocol all -SSLv2 -SSLv3.
- Restart httpd:
- Disable SSLv3. ...
- Apply the latest WLS PSU. ...
- Enable JSSE on 10.3.6. ...
- Update JDK to latest JDK. ...
- Remove weak ciphers you may have manually configured, which may now be a non-recommended value.
When CBC mode of encryption is used, there is simple birthday attack in which after 2n/2 blocks of data are encrypted with the same key, a collision between two ciphers blocks are expected. A collision in the output would mean that the input is same.